Summary
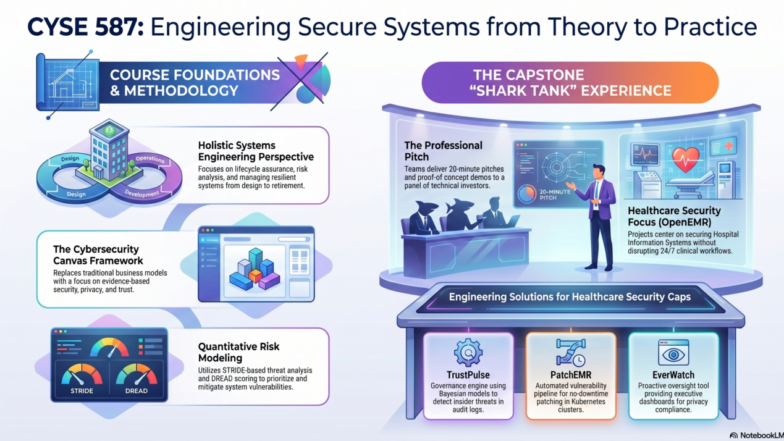
CYSE 587/SYST 687 & CYSE 787 is a course led by George Mason University’s (GMU) Cyber Security Engineering faculty. The course focuses on designing and engineering secure cyber-physical systems, with projects involving vulnerability assessments, security threat analysis, and defense strategies for complex systems like Supervisory Control and Data Acquisition (SCADA) or industrial control systems (ICS).
Students will also develop technical and professional skills through their project work.
CYSE 587 and SYST 687 students work in Teams. CYSE 787 students design and develop their projects on their own.
01/05/2026 (07:42)
This Google Notebook LM video explainer (Classic styel) was generated from the GMU CYSE 587 Spring 2026 category without any additional prompts or edits.
OnAir Post: CYSE 587/SYST 687 & CYSE 787 (Spring 2026)
News
CYSE 587 Shark Seminar
On May 6, 2026 at 4:30 PM, Dr. Alexandre De Barros Barreto’s CYSE Shark Tank – Cybersecurity Innovation Seminar will present their shark tank seminar presentations! Each team will present for twenty minutes before a panel of sharks began to ask their questions.
Event Details
- Location: Nguyen Engineering Building, Room 1103
- Virtual Attendance: The Zoom room will open at 4:20 PM for those joining remotely.
- Address: 4400 Patriot Cir, Fairfax, VA 22030
Go here to learn more about the course, the student projects, and the Shark panel.
About
CYSE 587: Cyber Security Systems Engineering. 3 credits.
This course addresses cyber security from the standpoint of systems engineers. It introduces core principles for the design and management of resilient and robust systems throughout their complete lifecycle.
Topics include but are not limited to lifecycle assurance of systems, risk analysis, models for secure systems development and management, gap analysis, quantitative methods for cyber security, and special topics in cyber security.
The course also covers distinct technologies for assessing system vulnerabilities, measuring and modeling risk, reducing uncertainty in risk management, and others.
Target audience consists of engineers who want to expand their skill sets to better align with the demands of current cyber security jobs, as well as those who intent to work on cyber security research. Cyber security professionals would also benefit from the course by being exposed to a systems engineering, holistic perspective on cyber security design, development, and management.
Offered by Cyber Security Engineering. May not be repeated for credit. Equivalent to CYSE 787, SYST 687, SYST 787.
Registration Restrictions:
Enrollment limited to students with a class of Advanced to Candidacy, Graduate, Junior Plus, Non-Degree or Senior Plus.
Students in a Non-Degree Undergraduate degree may not enroll.
Schedule Type: Lecture
Grading:
This course is graded on the Graduate Regular scale.
Videos
GMU CYSE 587 Spring 2026- video explainer (version 1)
May 1, 2026 (07:42)
This Google Notebook LM video explainer (Classic styel) was generated from the GMU CYSE 587 Spring 2026 category without any additional prompts or edits.
GMU CYSE 587 Spring 2026- video explainer (version 2)
May 6, 2026 (07:00)
By: GMU Cyber
Dr. Alexandre Barreto’s Intro
May 6, 2026 (09:05)
What is the CYSE Shark Tank – Cybersecurity Innovation Seminar?
- Inspired by the popular TV show Shark Tank
- Capstone-style event in which student teams from CYSE 587/787 Cyber Security System Engineering
- Focus on the application of the KEEN entrepreneur framework.
- Hospital Information System (OpenEMR).
587 & 687 Teams
TrustPulse
Source: GMU Cyber onAir Post
TrustPulse is a standalone, externally deployable governance and oversight engine designed to address the critical gap in operationalizing audit logs for small-to-medium healthcare organizations utilizing OpenEMR. While HIPAA mandates the recording and analysis of system activity, resource-constrained clinics often lack the structured workflows needed to translate raw telemetry into actionable security intelligence.
Integrating exclusively through approved read-only interfaces to ensure zero disruption to clinical workflows, TrustPulse utilizes a multi-layered analytical approach, combining STRIDE-based threat modeling, DREAD risk scoring, and probabilistic Bayesian and Fuzzy Logic models to prioritize anomalous access patterns and detect potential insider threats.
By providing a “human-in-the-loop”; review interface and generating exportable, documented evidence of compliance, the system empowers privacy officials to maintain rigorous oversight and defensible governance without requiring extensive cybersecurity expertise or modification of the underlying electronic health record architecture.
The Emergency Access Trust and Assurance Layer (EATAL)
Source: GMU Cyber onAir Post
The Emergency Access Trust and Assurance Layer (EATAL) is an external, read- only governance framework designed to oversee “break-glass” emergency overrides within OpenEMR-based Hospital Information Systems. While emergency overrides are essential for uninterrupted patient care in clinical settings, they shift the security burdenfrom preventive access controls to post hoc auditability, often leaving Protected Health Information (PHI) vulnerable to insider misuse.
EATAL addresses this accountability gap by ingesting raw audit telemetry and applying risk-informed scoring to the specific context of each override, effectively differentiating legitimate emergency care from unauthorized data access. By utilizing threat propagation modeling and quantifiable success criteria, such as a 50% reduction in manual audit review volume, the system provides clinical and compliance officers with actionable intelligence and structured evidence packages.
Ultimately, EATAL enhances the trust boundary in healthcare environments by providing rigorous, non-blocking oversight that ensures regulatory compliance with HIPAA and NIST standards without disrupting critical medical workflows.
PatchEMR
Source: GMU Cyber onAir Post
PatchEMR is an automated vulnerability management and decision-support pipeline designed to secure OpenEMR deployments without disrupting the 24/7 uptime requirements of clinical environments. Recognizing that unpatched systems remain a primary vector for healthcare data breaches and potential patient harm, PatchEMR operates as an external orchestration layer that continuously monitors security weaknesses.
The system automatically retrieves OpenEMR container images, performs deep component scanning with industry-standard tools like Trivy, and uses an AI threat broker to synthesize complex CVE data into actionable executive summaries for IT administrators. By integrating a Role-Based Access Control (RBAC) enforcer to manage deployments within Kubernetes clusters, PatchEMR facilitates a "no-downtime" patching strategy that upholds the integrity of the core Electronic Health Record (EHR) code.
Ultimately, the system bridges the gap between technical vulnerability disclosure and clinical operational safety, aiming for an 80% surface rate of known CVEs within 24 hours to ensure continuous protection of medical infrastructure and patient data.
EverWatch
Source: GMU Cyber onAir Post
EverWatch is a standalone, external cybersecurity governance tool designed to provide proactive oversight of OpenEMR-based Hospital Information Systems. While healthcare environments generate vast amounts of audit telemetry, compliance and security teams often struggle to transform these logs into actionable intelligence, leading to delayed detection of privacy violations and insider threats.
Operating strictly through approved read-only interfaces to ensure zero disruption to mission-critical clinical workflows,
EverWatch automatically correlates system activity to identify unusual access patterns, such as bulk record viewing or off-hours data access. By applying a risk-informed prioritization logic and a STRIDE-based threat analysis, the system produces executive- level dashboards and plain-language evidence summaries that support human-in-the- loop decision-making.
Ultimately, EverWatch strengthens the hospital's trust boundary and regulatory compliance posture by reducing manual audit-review time and providing
early-warning indicators of potential misuse without modifying the underlying EMR architecture.
Evaluations

Shark Panel Email
Dear Sharks,
Thank you for committing your time and expertise to evaluating our Cybersecurity Systems Engineering capstone projects. Your participation is vital in bridging the gap between academic theory and high-stakes professional practice.
The Goal of the Event: The Shark Tank–style seminar is the final deliverable for our graduate students. The goal is for each team to present a professional project pitch that justifies their architectural decisions, defends their threat modeling, and articulates the value of their solution within a real-world Hospital Information System (OpenEMR). This event simulates a real-world environment in which engineers must defend their technical reasoning to senior stakeholders and decision-makers under time constraints.
How it Works
- Format: Each team has 20 minutes for their presentation and a working proof-of-concept demonstration.
- Time: 04:30 pm – 7:30 pm (EST – DC Time)
- Participation: To accommodate different schedules and locations, you may participate either in person at our campus or online via the provided link.
- In person: Nguyen Engineering Building 1103 (GMU – Fairfax Campus)
- Online: https://gmu.zoom.us/j/99002964828?pwd=svZxUSOF0Xo45KWeM3Y7Qm5aqcFJif.1&from=addon
- The Technical Investor Mindset: We ask that you adopt the role of a “technical investor.” While students need to be persuasive, your focus is on technical soundness, system-level reasoning, and the management of cybersecurity, trust, and governance risks. Despite the students being engineers, they were forced to adopt an Entrepreneur Mindset.
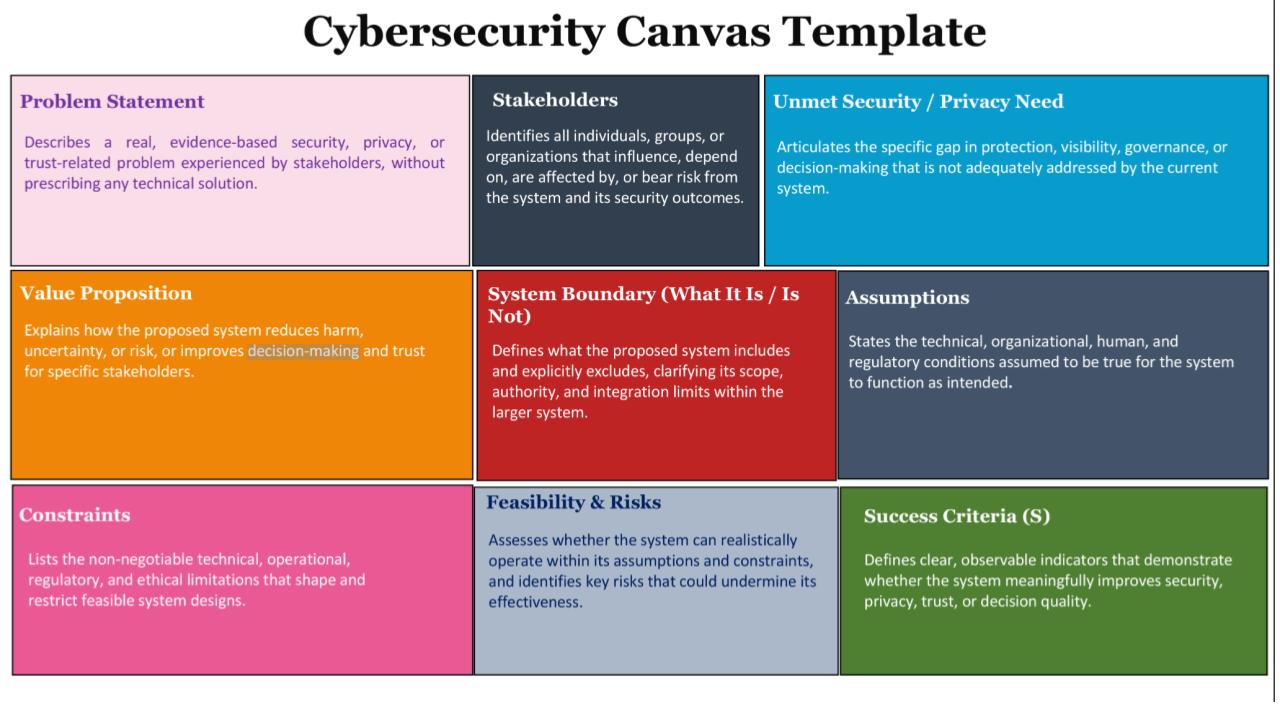
The Cybersecurity Canvas vs. Market Investigation: It is important to note that this “Shark Tank” differs from traditional business competitions. We are using the Cybersecurity Canvas (attached) framework rather than a standard business model.
- Not a Market Study: We are not evaluating market size, profit margins, or traditional “market investigation.”
- Problem Framing: The focus is on evidence-based security, privacy, and trust-related problems.
- Value Proposition: In this context, “Value” refers to risk reduction, harm prevention, and the improvement of decision-making and trust for specific healthcare stakeholders. We are looking into how the system manages the “pains” of cyber threats and operational failures.
Evaluation and Feedback: We have encouraged our students to prepare for rigorous, candid evaluations. Do not hesitate to be direct; these “crude” or blunt critiques are often the most valuable for engineering growth. The objective is to challenge their assumptions, expose gaps in their threat reasoning, and push them to refine their ideas as they move toward professional practice.
Attached you will find the evaluation rubric (Appendix 2), which covers:
- Problem Framing & Market Pain (from a security perspective)
- Value Proposition & Pitch Persuasiveness
- Technical Feasibility & Architecture
- Cybersecurity & Privacy Effectiveness
- Threat & Risk Reasoning
- Proof of Concept Demo
- Professionalism
Finally, in the attachment, you can find the abstract of each group that will present the work during the event.
We look forward to your insights and to a session of robust technical exchange.
Best regards,
Prof. Alexandre Barreto, Ph.D.
Canvas Business Template
Shark Tank Panelist Performance Evaluation
…