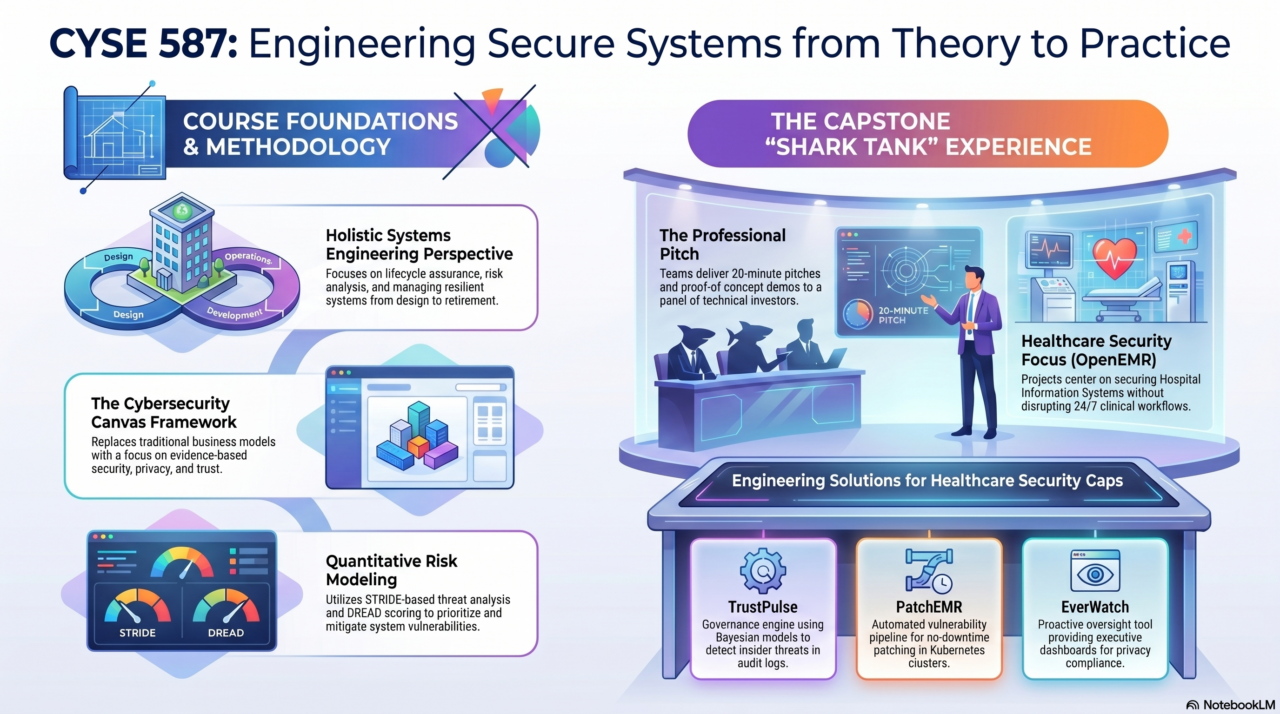
CYSE 587/SYST 687 & CYSE 787 is a course led by George Mason University’s (GMU) Cyber Security Engineering faculty. The course focuses on designing and engineering secure cyber-physical systems, with projects involving vulnerability assessments, security threat analysis, and defense strategies for complex systems like Supervisory Control and Data Acquisition (SCADA) or industrial control systems (ICS).
Students will also develop technical and professional skills through their project work.
CYSE 587 and SYST 687 students work in Teams. CYSE 787 students design and develop their projects on their own.
01/05/2026 (07:42)
https://youtu.be/oSwAS7upbw0
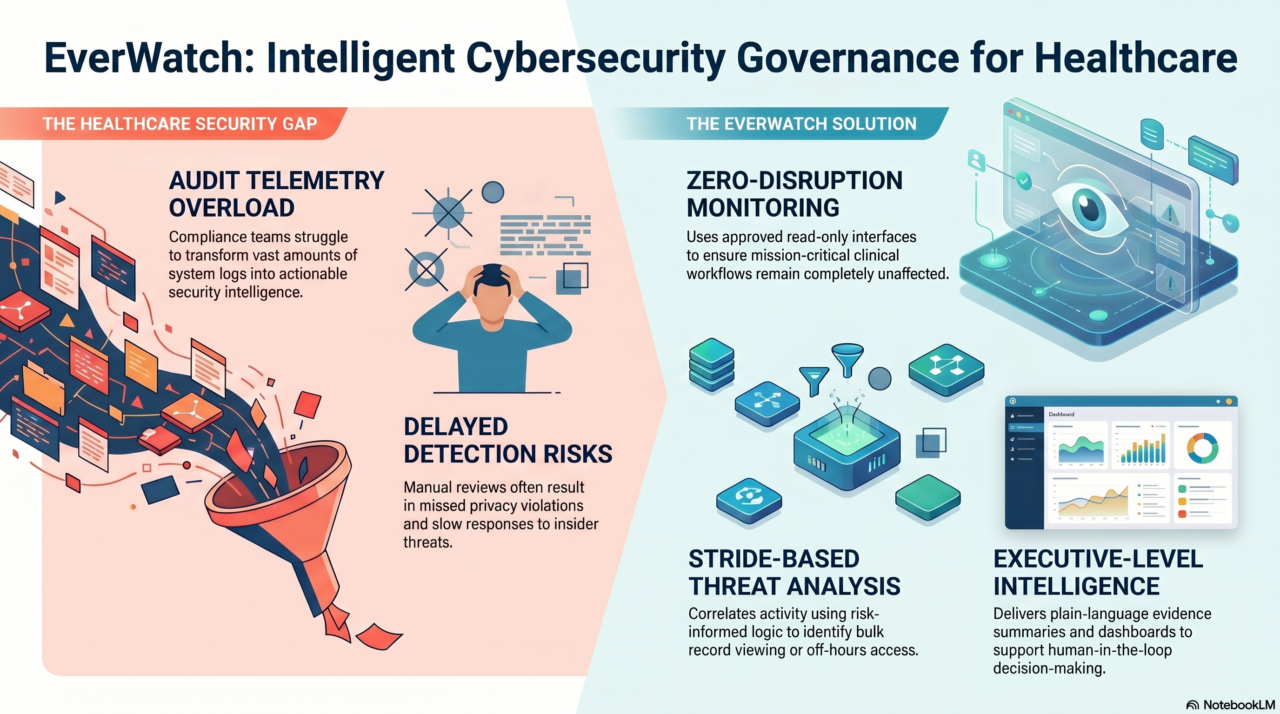
This Google Notebook LM video explainer (Classic styel) was generated from the GMU CYSE 587 Spring 2026 category without any additional prompts or edits.
OnAir Post: CYSE 587/SYST 687 & CYSE 787 (Spring 2026)